BLUF
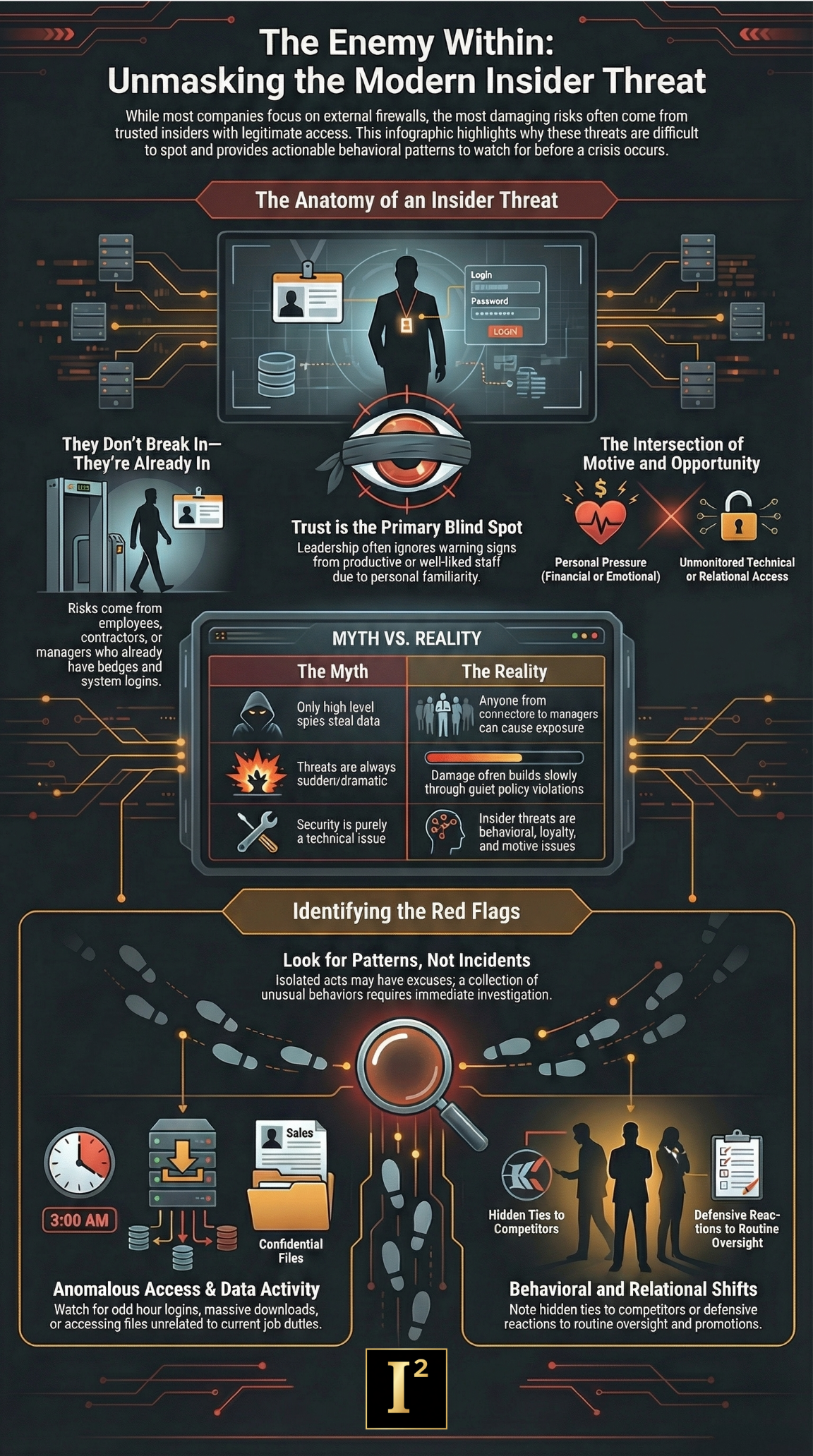
The most dangerous threat to your company may already have a badge, a login, a trusted title, and a reason nobody wants to question them. Insider threats do not always look like sabotage or espionage. More often, they show up as quiet access misuse, data leakage, policy violations, hidden conflicts, suspicious relationships, and trusted people doing damage from the inside before leadership realizes there is a real problem.
Most companies are built to defend against outsiders
That makes sense.
Outside attackers are easier to imagine. They are easier to fear. They fit the standard security story.
Unknown intruder.
Phishing attempt.
External breach.
Competitor pressure.
Cyber threat from somewhere beyond the firewall.
But many of the most damaging risks do not start outside the company.
They start inside it.
An employee with access.
A contractor with visibility.
A manager with influence.
A trusted insider who knows the systems, the people, the blind spots, and the exact places where no one is paying close attention.
That is what makes insider threats dangerous.
They do not have to break in.
They are already in.
An insider threat is not always dramatic
This is where companies get it wrong.
When people hear the phrase insider threat, they often think of a worst case scenario.
Stolen trade secrets.
Massive data theft.
Sabotage.
Corporate espionage.
A disgruntled employee wiping systems.
A bad actor feeding information to a competitor.
That can happen.
But the real problem is broader than that.
Insider threats also include:
- Misuse of access
- Unauthorized sharing of sensitive information
- Concealed relationships
- Quiet violations of policy
- Improper downloads or transfers
- Manipulation of records
- Undisclosed conflicts of interest
- Helping an outside party from the inside
- Using privileged knowledge for personal gain
- Behavior that creates legal, operational, or reputational exposure
The damage may build slowly.
It may not look criminal at first.
It may be written off as poor judgment, office politics, or a one time lapse.
That is often how it survives.
Why insider threats are so hard to spot
Trust gets in the way
The people with the most dangerous access are often the people the company relies on.
They know the systems.
They know the process.
They have been around.
They are productive.
They are familiar.
They may even be well-liked.
That creates hesitation.
Leadership does not want to believe the problem could be coming from someone already inside the circle.
So the warning signs get softened.
Access looks routine until it does not
A lot of insider threat behavior blends into normal work activity.
File access.
Email traffic.
System usage.
Vendor contact.
Document review.
Late night logins.
Downloads.
Internal searches.
Travel.
Meetings.
On paper, all of it may look explainable.
The danger is not always in one single act.
It is often in the pattern.
Companies separate security from behavior
This is a major mistake.
Insider threats are not only technical issues. They are behavioral, access, loyalty, judgment, and motive issues.
A company can have strong cybersecurity controls and still miss the person inside the business who is misusing trust, privilege, or relationships.
If the investigation only looks at logs and never looks at conduct, the story stays incomplete.
The insider threat may not be who leadership expects
Not every insider threat comes from a senior executive or a known problem employee.
Sometimes it is:
- A respected employee under financial pressure
- A departing team member taking more than they should
- A contractor with too much system access
- A manager protecting someone they should have reported
- An employee with a side relationship to a vendor or competitor
- A trusted administrator changing records quietly
- A worker who feels slighted and starts pushing boundaries
- A person who believes company information is theirs to use
This is why titles do not tell you enough.
Tenure does not tell you enough.
Performance alone does not tell you enough.
Risk often sits where trust is highest and oversight is weakest.
Common signs of insider threat activity
Insider threats usually leave signals before they leave wreckage.
The problem is that those signals are often dismissed until something serious happens.
Watch for patterns like:
- Accessing information outside normal job needs
- Repeated downloads or transfers of sensitive material
- Unusual interest in systems, records, or files unrelated to assigned work
- Login activity at odd times without a business reason
- Sudden attempts to bypass normal approval channels
- Defensive behavior about routine oversight
- Private communications that avoid normal business systems
- Hidden relationships with vendors, competitors, or third parties
- Abrupt behavior changes after discipline, missed promotion, or conflict
- Taking screenshots, printing unusual volumes, or copying files
- Unauthorized use of personal devices or storage methods
- Attempts to conceal activity, rename files, or alter records
- Resistance to offboarding controls or access limits
- Knowledge of internal information showing up where it should not
One of these signs alone may not prove much.
Several of them together deserve immediate attention.
Insider threats often sit at the intersection of motive and opportunity
This is what companies need to understand.
A person becomes dangerous when two things come together:
They have a reason.
They have access.
The reason may be financial.
It may be emotional.
It may be career-driven.
It may be about revenge, loyalty to someone else, pressure from outside, or the belief that they can get away with it.
The access may be technical, operational, administrative, or relational.
Once those two things come together, the risk changes quickly.
That is why insider threat investigations cannot focus solely on the system or the person. They have to examine both.
These cases are not always about stolen data
Data theft matters. Trade secret loss matters. But insider threats can hurt a company in other ways too.
They can:
- Expose litigation strategy
- Compromise internal investigations
- Leak pricing or bid information
- Undermine procurement integrity
- Manipulate vendor decisions
- Damage employee trust
- Create compliance failures
- Trigger reputational harm
- Help fraud survive longer
- Interfere with evidence
- Alter records that decision makers rely on
Sometimes the insider threat is not stealing information for a competitor. Sometimes, they are quietly poisoning the integrity of the company from within.
That can be just as destructive.
The danger grows when leadership waits too long
This is where many companies lose control.
Something feels off.
A supervisor notices odd behavior.
A team member raises a concern.
An access issue appears.
A strange relationship comes to light.
A file turns up where it should not be.
But there is hesitation.
Maybe it is nothing.
Maybe there is an innocent explanation.
Maybe it will create a bigger problem to look too closely.
Maybe the person is important.
Maybe leadership wants more proof before acting.
That delay is expensive.
Evidence gets harder to preserve.
The insider gets time to adjust.
Stories tighten.
Records move.
Devices change.
Other people get pulled in.
The damage spreads.
The longer leadership treats a real warning sign like a personal annoyance, the more likely it becomes a legal and operational problem.
What a real insider threat investigation should examine
A serious insider threat investigation is not a fishing expedition. It should be structured, disciplined, and tied to facts.
That may include:
- Access patterns
- Role based need versus actual behavior
- Timeline development
- Relationship mapping
- Communications review within legal bounds
- Vendor or competitor connections
- Document handling patterns
- Physical presence and movement
- Policy violations
- Changes in conduct
- Digital footprint contradictions
- Motives tied to disputes, money, pressure, or outside interests
The point is not to assume guilt.
The point is to establish what is actually happening before the company makes the wrong move or no move at all.
Why independent investigations matter
Insider threat matters are hard to handle internally for one simple reason.
Too many people already know each other.
Managers may be conflicted.
HR may be cautious.
IT may see only part of the picture.
Legal may need facts before advising next steps.
Executives may be too close to the people involved.
That is where independent investigative work matters.
A neutral investigation can separate suspicion from evidence, connect behavior to access, identify the actual scope of risk, and document what leadership needs to know without turning the matter into rumor, panic, or office theater.
Not every concern turns out to be an insider threat
This matters too.
Sometimes the suspicious behavior has a legitimate explanation.
Sometimes the odd access was work-related.
Sometimes the relationship was disclosed but poorly documented.
Sometimes, the process problem matters more than the person.
That is why investigation matters.
A good investigation does not force a conclusion. It tests the concern and shows leadership what is true.
That protects the company.
It also protects innocent people from reckless accusations.
What companies should do now
Treat insider threat concerns as business risk, not just HR discomfort or technical noise.
Do not wait for a catastrophic event to take the issue seriously.
Look at patterns, not isolated excuses.
Question access that does not make sense.
Pay attention when behavior changes around conflict, departure, or pressure.
Take hidden relationships seriously.
Move early enough to preserve facts.
The goal is not paranoia.
The goal is clarity before the risk becomes a crisis.
Bottom line
The insider threat sitting inside your company right now probably does not look like a headline. They look familiar. They look trusted. They look explainable. That is why they are dangerous.
Insider threats succeed when companies rely too heavily on trust, separate behavior from access, and dismiss warning signs until the problem becomes too large to contain quietly. The companies that handle these risks well do not wait for perfect proof or public damage. They investigate early, protect the facts, and act before a trusted insider turns a manageable risk into a legal, operational, and reputational disaster.
That is how serious organizations protect themselves against threats already inside the building.