BLUF
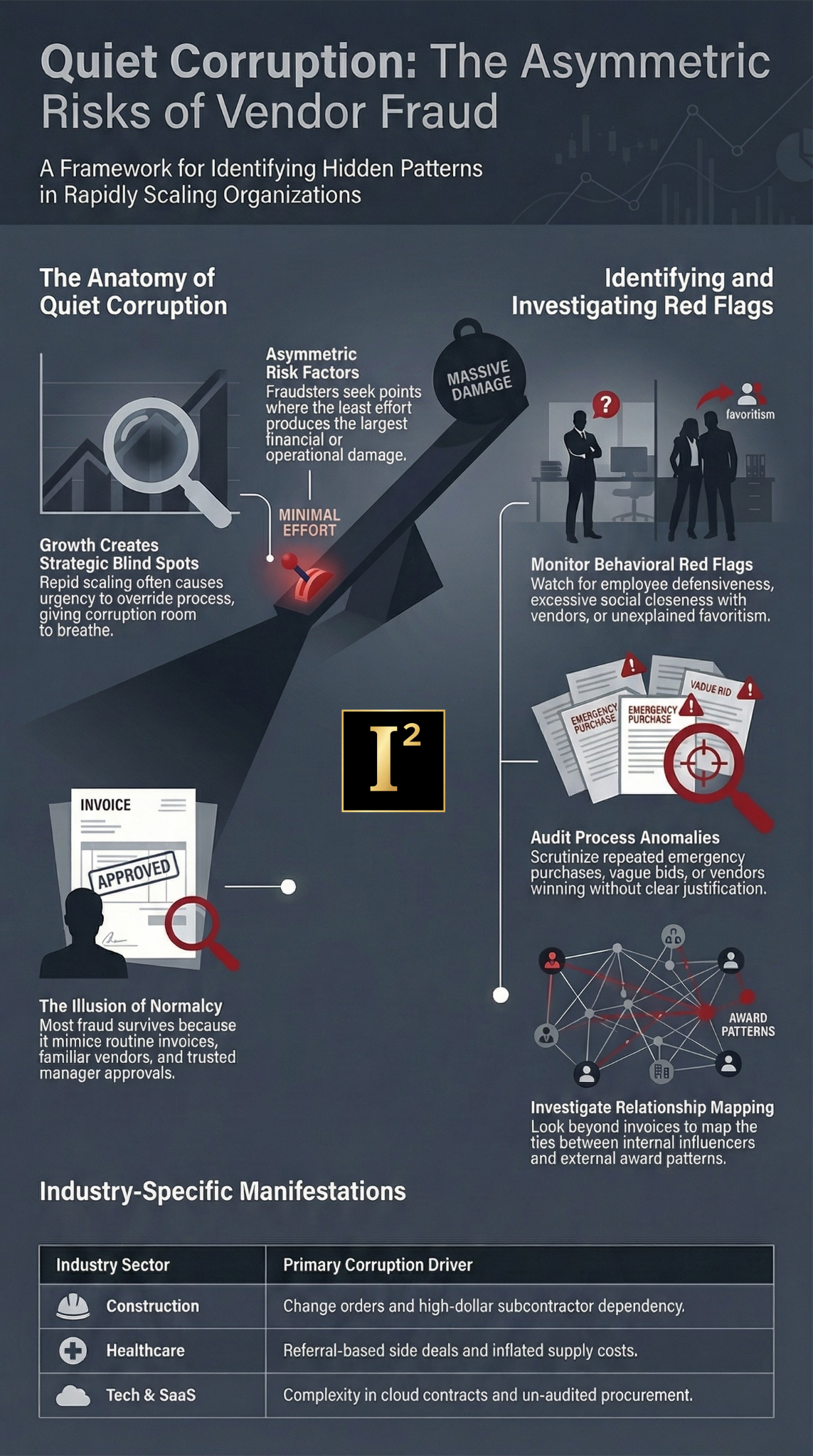
Vendor fraud rarely starts with a dramatic theft or a fake invoice that anyone could spot in five seconds. It usually starts with trust, speed, weak oversight, a favored relationship, and one person inside the company quietly steering money, approvals, or access where it does not belong. In growing companies, that risk expands fast because procurement scales before controls mature, vendor lists grow before they are tested, and executives stay focused on revenue while quiet corruption builds underneath them. Using asymmetric analysis, the real question is not only where money is being lost. It is where a bad actor needs the least effort to create the most damage with the lowest chance of being challenged.
Growth creates blind spots that corruption loves
Most companies do not become vulnerable because of careless leadership. They become vulnerable because growth changes the operating environment faster than internal discipline catches up.
The company adds locations.
New vendors come in.
Teams expand.
Approvals get delegated.
Managers get more discretion.
Finance gets stretched.
Founders stop touching every decision.
Urgency starts beating process.
That is the moment when quiet corruption gets room to breathe.
Vendor fraud does not need chaos. It needs just enough speed, trust, and fragmentation for nobody to see the full pattern.
What asymmetric analysis shows in vendor fraud cases
Most internal reviews ask a simple question.
Where is the fraud?
That is useful, but it is not enough.
Asymmetric analysis asks a harder question.
Where can a dishonest insider or corrupt vendor apply the smallest amount of manipulation to produce the largest operational, financial, legal, or reputational effect?
That changes the analysis.
- It pushes leadership to look for:
- Low visibility decision points
- People with outsized influence but limited review
- Processes where one exception becomes a habit
- Vendors that sit close to money, access, data, or critical operations
- Departments where speed is rewarded more than documentation
- Relationships where loyalty replaced verification a long time ago
- Fraud is asymmetric because the bad actor does not need to control the whole company. They only need to find the right weak point.
Quiet corruption usually looks normal at first
That is why it survives.
The invoice looks routine.
The vendor is familiar.
The pricing increase has an explanation.
The urgent work order gets approved.
The same contractor keeps winning.
The manager says they trust them.
The paperwork exists, just not enough of it.
Nobody wants to be the person slowing growth over something that feels small.
That is how corrupt systems form. Not through one giant act, but through repeated normal looking decisions that stop getting questioned.
What vendor fraud and kickbacks often look like in practice
Kickback schemes are rarely labeled as kickbacks. They hide inside ordinary business behavior.
A manager keeps steering work to the same outside firm.
A vendor keeps getting approved despite weak performance.
Pricing stays high without challenge.
Bid competition looks thin or staged.
Emergency purchases keep bypassing review.
A family member or friend sits behind an LLC no one examined.
Gifts, favors, travel, entertainment, consulting fees, referral arrangements, inflated change orders, and side agreements blur the line between relationship and corruption.
In a growing company, people often mistake familiarity for proof of legitimacy.
It is not.
Ten sectors where vendor fraud and quiet corruption hit differently
Construction and real estate development
This sector is built on change orders, subcontractors, scheduling pressure, material delays, and high dollar vendor dependency. That makes it fertile ground for inflated billing, rigged subcontractor awards, bid steering, fake urgency, and project manager kickback schemes.
One superintendent or project manager can quietly direct work to a preferred subcontractor, approve padded invoices, or normalize overbilling because no one above them clearly sees the daily field pattern to challenge it.
Healthcare and medical practices
Healthcare groups, clinics, and specialty practices often rely on outside billing firms, equipment vendors, staffing vendors, waste-disposal services, IT providers, and pharmaceutical relationships. Quiet corruption here may involve referral-based side deals, inflated supply costs, overordering, conflict-driven purchasing, or service contracts that exist because of personal relationships rather than value.
The damage is not just financial. It can also create compliance and patient trust issues.
Manufacturing and industrial operations
Manufacturers depend on raw materials, maintenance vendors, machine repair providers, logistics partners, tooling suppliers, and safety equipment vendors. Corruption often hides in sole source arrangements, padded maintenance bills, repeated emergency orders, inventory substitution, low quality inputs billed as premium materials, or procurement staff with undisclosed ties to suppliers.
The asymmetric risk here is brutal. A small, compromised vendor relationship can disrupt quality, margins, uptime, and customer trust all at once.
Technology companies and SaaS firms
Many leaders assume fraud risk in tech is mostly cyber-related. That is too narrow. Growing tech companies often burn cash through software procurement, cloud contracts, outside developers, recruiting firms, marketing vendors, consultants, hardware resellers, and data providers.
Kickbacks can hide in vendor onboarding, commission structures, agency relationships, implementation work, and inflated subscription costs nobody audits because the business is moving too fast. In these environments, corruption often hides behind complexity.
Hospitality and restaurant groups
Restaurant groups, hotel operators, and hospitality businesses deal with food vendors, beverage contracts, maintenance providers, staffing agencies, linen services, cleaning vendors, and point of sale systems. A corrupt manager can create enormous leakage through preferred supplier relationships, low visibility inventory manipulation, false service calls, fake shortages, or local vendor collusion.
Because margins are tight, even modest fraud can do real harm quickly.
Logistics and transportation
Freight, fleet, warehousing, fuel, last-mile delivery, maintenance, and parts procurement create multiple opportunities for a vendor relationship. Fuel fraud, padded repair billing, false capacity claims, emergency routing decisions, and hidden side deals with local carriers all create opportunities.
The asymmetric feature in this sector is that one compromised node can affect cost, delivery reliability, contract performance, and claims exposure at the same time.
Professional services firms
Law firms, accounting firms, consulting groups, engineering firms, and advisory businesses often assume they are too sophisticated for vendor corruption. They are not. These firms still buy IT services, office buildout work, staffing, discovery vendors, trial support, software, outsourced marketing, and facilities services.
Fraud here often persists because the company sees itself as low-risk. That confidence can make weak procurement habits almost invisible.
Retail and ecommerce
Retailers and ecommerce companies rely on fulfillment partners, packaging vendors, digital ad agencies, marketplace consultants, payment tools, customer service providers, and supply chain vendors. Kickbacks may involve warehousing contracts, shipping rate manipulation, inventory substitutions, marketing overbilling, return fraud arrangements, or favored third party service providers.
Because many of these businesses scale through outsourced relationships, the risk multiplies as they grow.
Private equity portfolio companies
Portfolio companies are especially exposed during rapid scaling, integration, leadership transition, and margin pressure. New executives may rely on inherited vendor ecosystems they do not fully understand. Legacy relationships often stay in place because nobody wants disruption during a transition.
That creates the perfect opening for quiet corruption already embedded in procurement, facilities, staffing, technology, logistics, or construction relationships.
Nonprofits and mission-driven organizations
Many people underestimate corruption risk in nonprofits because the mission creates an assumption of trust. That can be a serious mistake. Event vendors, grant related contractors, facilities vendors, consultants, technology providers, fundraising agencies, and staffing firms can all become channels for favoritism, inflated billing, or insider relationships.
The reputational damage can be worse here than the dollar loss because donor trust is fragile once corruption becomes visible.
Ten specific situations where the risk spikes
Founder-led companies moving into middle management
The founder used to know every vendor. Now they do not. A newly empowered manager has influence but limited oversight. That is a prime condition for bid steering and preferred vendor abuse.
Rapid expansion into new markets
New regions mean new local vendors. Local relationships often get approved fast because the company wants speed. That urgency lowers scrutiny.
Procurement without true segregation of duties
When one person can suggest the vendor, help approve the vendor, confirm the work, and influence the payment, the fraud path is short and easy.
Repeated emergency purchases
Emergency purchasing is a corruption magnet because urgency weakens documentation and discourages pushback.
High reliance on one vendor without review
Sometimes the relationship is legitimate. Sometimes it has simply never been challenged. Either way, concentration without testing creates vulnerability.
Family-owned businesses with informal controls
These companies often run on loyalty and verbal approvals. That can make hidden vendor favoritism incredibly easy to disguise.
Mergers and post acquisition integration
Inherited vendors often slide through because the acquiring company assumes someone else vetted them already.
Cash flow stress and margin compression
When financial pressure hits, corrupt actors know leadership is distracted. That is when inflated invoices and hidden side arrangements often expand.
Decentralized operations
Multiple locations and local managers create the perfect environment for small scale corruption that stays below central visibility.
Outsourced back office functions
If accounts payable, facilities coordination, staffing, or procurement support are partially outsourced, visibility gaps can widen fast.
The anatomy of a kickback scheme
Most kickback schemes have a few recurring ingredients.
First, someone inside the company has influence.
Second, a vendor benefits repeatedly in ways that do not quite line up with objective performance or price.
Third, the internal advocate has a reason to protect the relationship.
That reason may be cash.
It may be gifts.
It may be favors.
It may be travel, entertainment, future employment, personal loyalty, hidden ownership, family ties, or quiet reciprocal benefits.
The money trail may be obvious.
More often, it is not.
That is why investigations must look at behavior, timing, influence, and relationship mapping, not just invoices.
Red flags leadership should stop rationalizing
Watch for patterns like these:
- The same vendor keeps winning without strong justification
- Bids are vague, thin, or strangely similar
- Emergency work keeps going to one provider
- Pricing rises faster than the market with little pushback
- Documentation is always just incomplete enough to avoid clarity
- Employees get defensive about routine vendor questions
- There is social closeness between internal staff and outside vendors
- Performance complaints somehow never affect award decisions
- A vendor was selected before the formal process started
- Change orders keep turning a cheap job into an expensive one
- One person always pushes hard for the same outside firm
- Small gifts and hospitality seem excessive for the relationship
A cluster of these signs deserves attention.
Why growing companies miss the pattern
They miss it because each piece looks survivable on its own.
A little overbilling.
A little favoritism.
A few weak controls.
One trusted manager.
One familiar contractor.
One market where oversight is thinner.
One exception for speed.
But corruption is cumulative.
Asymmetric risk means the bad actor wins by spreading small abnormalities across a system not designed to see the whole pattern at once.
Leadership keeps seeing isolated issues.
The corrupt actor sees one working model.
What a real investigation should examine
A serious vendor fraud investigation should look beyond the invoice.
It should examine:
- Award patterns
- Bid quality and vendor selection logic
- Approval chains
- Relationship mapping between insiders and vendors
- Pricing consistency across vendors, sites, and time periods
- Scope change patterns
- Payment timing
- Communications behavior within legal and policy limits
- Performance gaps versus continued vendor preference
- Ownership, shell entities, and undisclosed affiliations
- Digital footprint and public records tied to internal and external actors
The question is not simply whether the company paid too much. The question is whether someone manipulated trust and process for personal benefit.
Quiet corruption creates more than financial loss
The damage may show up as:
- Margin erosion
- Project overruns
- Quality failures
- Compliance problems
- Insurance disputes
- Employee morale damage
- Leadership credibility loss
- Regulatory exposure
- Client trust erosion
- Litigation
A company may think it has a procurement issue when in reality it has a governance issue, a culture issue, and a corruption issue sitting in the same room.
Why this gets worse the longer it runs
Time helps the corrupt actor.
The vendor gets embedded.
The internal advocate gains influence.
Paper trails get normalized.
Other employees stop questioning the pattern.
Losses spread across accounts and periods.
The relationship becomes operationally inconvenient to challenge.
That is why companies often wait too long. By the time the pattern feels undeniable, the vendor is woven into the business and the internal damage is harder to isolate.
What disciplined leaders do differently
They do not wait for a confession.
They do not assume familiarity means legitimacy.
They do not treat procurement anomalies as administrative noise.
They look for asymmetry. Where can one insider, one vendor, or one weak control distort too much value with too little resistance?
That is the right question.
Because fraud does not need to own the whole system.
It only needs one protected channel that nobody wants to examine too closely.
Bottom line
Vendor fraud, kickbacks, and quiet corruption inside growing companies rarely announce themselves loudly. They build inside trusted relationships, speed based decisions, weak approval structures, and the natural blind spots that come with expansion. Through asymmetric analysis, the issue becomes clearer. The greatest risk is not always where the company spends the most money. It is where one compromised relationship can quietly shape awards, pricing, performance, and internal decisions with almost no resistance.
That is where the damage multiplies.
That is where serious leaders need to look.
That is where a disciplined investigation can stop a quiet form of corruption before it becomes part of how the company operates.